Hackers have simply pulled off what some are calling the most important software program provide chain assault in historical past—and it ought to scare the hell out of anybody who makes use of crypto.
The breach hit core JavaScript libraries like chalk, strip-ansi, and color-convert—packages so foundational they’re virtually digital plumbing. Collectively, these libraries are downloaded billions of instances each single week, quietly operating inside all the things from net apps to developer instruments. Most devs by no means set up them immediately, however they lurk deep in dependency timber. That’s why this assault is systemic.
What Occurred
Based on multiple security reports, attackers compromised the NPM account of a well known developer, slipped malicious code into these libraries, and shipped them straight into the worldwide software program bloodstream. The payload? A crypto-clipper—malware that swaps out pockets addresses mid-transaction, silently diverting funds to the attacker.
When you’ve ever copied a pockets deal with, pasted it right into a subject, and hit “Ship,” that is your nightmare state of affairs. The code hijacks the vacation spot deal with, and until you manually double-check on a {hardware} pockets, your funds are gone.
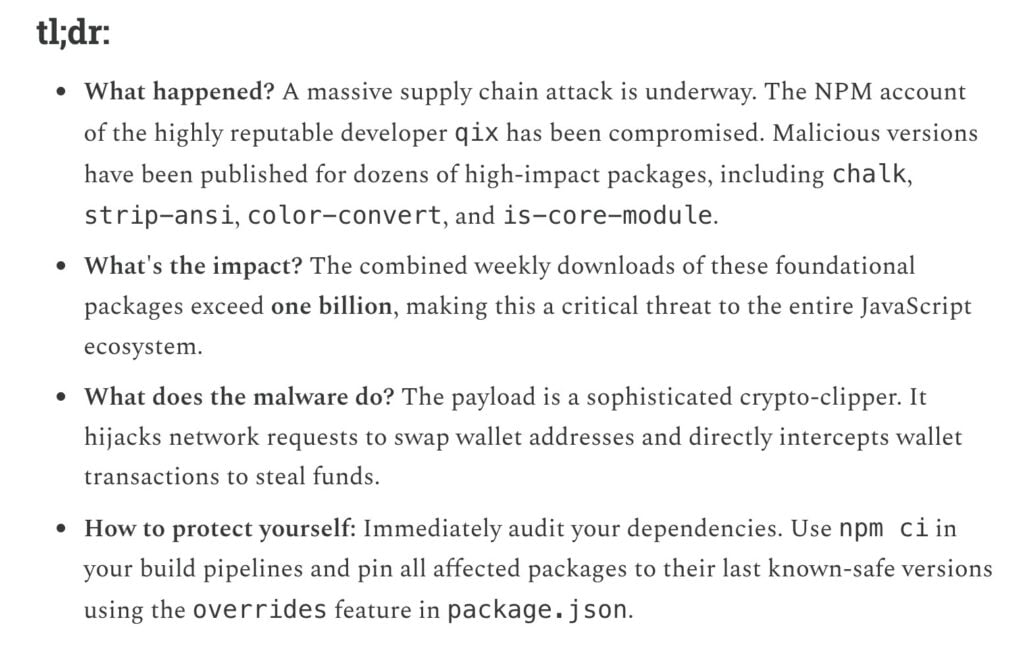
The TLDR from safety researchers, supply: Observations
Why This Issues
- For crypto customers: When you depend on software program wallets, you’re uncovered. {Hardware} wallets that pressure you to bodily verify each transaction stay the gold commonplace for safety.
- For builders: The assault didn’t simply compromise apps constructed by careless coders. It poisoned libraries so elementary that even probably the most diligent devs are affected. You don’t have to put in these packages immediately—your dependencies already did it for you.
- For the open-source ecosystem: NPM is principally the app retailer of the JavaScript world. It’s additionally a single level of failure. A lone compromised developer account simply weaponized code that billions of individuals not directly belief.
The Unanswered Questions
It’s nonetheless unclear whether or not the malware goes additional—some researchers speculate it may additionally try and steal seed phrases immediately. If true, this could elevate the hack from “clipper assault” to “full-on pockets drain.”
It’s one other brutal reminder that our total digital infrastructure rests on volunteer-maintained open-source codebases—usually written by one individual of their free time. Chalk isn’t glamorous, however it’s in all places. When attackers compromise one thing this elementary, the fallout ripples throughout all the web.
Crypto simply occurs to be the juiciest goal as a result of it’s instantaneous cash, no chargebacks, no intermediary. However make no mistake: the actual disaster is that the worldwide software program provide chain is held along with duct tape and belief.
Ship transactions with warning till that is resolved.
Jason Jones Jason Jones Read More