Microsoft has recognized a brand new distant entry trojan (RAT) named StilachiRAT, which they are saying poses a big risk to cryptocurrency customers.
First detected in November 2024, this malware employs superior methods to evade detection, preserve persistence, and exfiltrate delicate information from compromised methods.
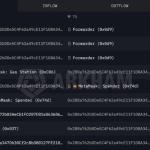
Notably, it particularly targets cryptocurrency belongings by scanning for configuration information of 20 completely different pockets extensions inside the Google Chrome browser. These focused wallets embrace MetaMask, Belief Pockets, Coinbase Wallet, Phantom Pockets, BNB Chain Pockets, OKX Pockets, and others.
Capabilities and Targets
StilachiRAT is designed to conduct intensive system reconnaissance, accumulating info comparable to working system particulars, {hardware} identifiers, BIOS serial numbers, digital camera presence, lively Distant Desktop Protocol (RDP) periods, and working graphical consumer interface functions.
Along with cryptocurrency theft, StilachiRAT can extract and decrypt credentials saved in Google Chrome, monitor clipboard content material for delicate information comparable to passwords and cryptocurrency keys, and observe lively home windows and functions. The malware additionally screens RDP periods by capturing foreground window info and duplicating safety tokens to impersonate customers, doubtlessly facilitating lateral motion inside networks.
Persistence and Evasion Strategies
To take care of persistence, StilachiRAT can function both as a Home windows service or a standalone element, using watchdog threads that monitor its presence and recreate its recordsdata if they’re eliminated. The malware establishes communication with its command-and-control (C2) servers utilizing generally used TCP ports like 53 and 443, permitting it to obtain instructions comparable to system reboots, log clearing, registry manipulation, software execution, and system suspension.
Microsoft says StilachiRAT employs numerous anti-forensic and evasion ways, together with clearing occasion logs to erase proof, detecting forensic instruments and digital machines to keep away from evaluation, and implementing sandbox-evading behaviors to forestall detection. These stealthy approaches make it tough to detect and take away as soon as a system is compromised.
Mitigation Methods
To guard towards StilachiRAT, safety specialists suggest a number of measures:
-
Hold software program and working methods up to date: Usually apply patches to handle identified vulnerabilities.
-
Use respected safety software program: Implement complete safety options that embrace antivirus and endpoint detection and response capabilities.
-
Allow Multi-Issue Authentication (MFA): Including an additional layer of safety can stop unauthorized entry.
-
Train warning with downloads and hyperlinks: Keep away from unverified downloads and be cautious of clicking on suspicious hyperlinks.
-
Monitor system logs: Usually overview logs for unauthorized adjustments or uncommon exercise.
For cryptocurrency customers, it’s significantly essential to concentrate on the dangers related to browser-based wallets, which retailer non-public keys in software program and are weak to malware assaults.
Safety specialists emphasize that the most secure approach to shield crypto holdings is to retailer non-public keys in a {hardware} pockets or with a qualified custodian. In contrast to software-based wallets, {hardware} wallets retailer non-public keys in a safe chip, require bodily affirmation for transactions, and are proof against clipboard hijacking and keylogging assaults.
David McNickel David McNickel Read More